Join our experts at WWHF @ Mile High! WWHF brings together cutting-edge technical talks, immersive workshops and labs, and countless opportunities to connect with industry experts, including Cobalt Strike’s own Steve Salinas and Austin Hudson. Stop by Booth #12 to connect and talk shop about the latest in offensive security. Hope to see you there! […]
Read More… from Wild West Hackin’ Fest @ Mile High 2026
This blog is all about experimenting and having fun with the new CS REST API and the generative AI ecosystem. We’ll demonstrate how we used Claude Desktop and its Model Context Protocol (MCP) integration to automate and orchestrate attacks through the CS REST API. We will also share the following internal (vibe-coded) experiments, intended to […]
Read More… from Me, Myself and AI: Internal Experiments with the CS REST API
Cobalt Strike 4.12 introduces: Release blogs can be found here and release notes here. Are you ready to take the next step? […]
Read More… from Cobalt Strike 4.12 in 1 Minute
The REST API was a major feature of the 4.12 release and forms part of a broader ongoing change in the Cobalt Strike ecosystem. Therefore, we wanted to dedicate a blog post to explain the rationale behind it, discuss the architecture, and provide hands-on examples to get our customers up and running. In addition to […]
Read More… from Release Out: Finally, Some REST

Cobalt Strike 4.12 is now available. We are excited to introduce a new look and feel for the Cobalt Strike GUI, a REST API, User Defined Command and Control (UDC2), new process injection options, new UAC bypasses, a new BOF API BeaconDownload for in-memory buffers, and new drip loading Malleable C2 options. Additionally, we have overhauled […]
Read More… from Cobalt Strike 4.12: Fix Up, Look Sharp!
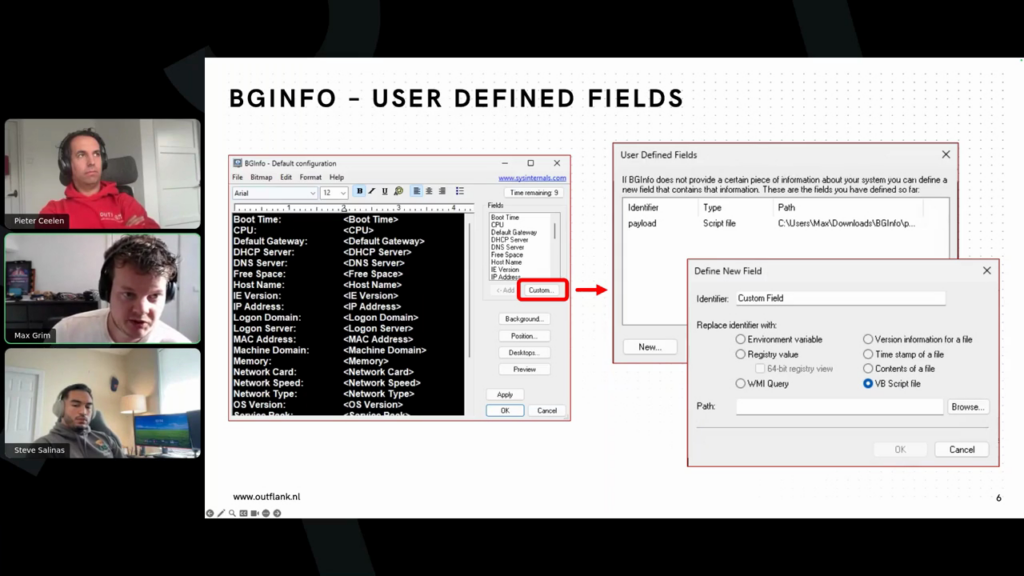
Watch a technical walkthrough of Cobalt Strike’s advanced capabilities for post-exploitation and adversary simulation, or our new Cobalt Strike Research Labs. In the session, Cobalt Strike developers and researchers will demonstrate usage of the product and show the advanced evasion and customization of Cobalt Strike through hands-on demos. The session will be presented by Cobalt […]
Read More… from Cobalt Strike Technical Demo
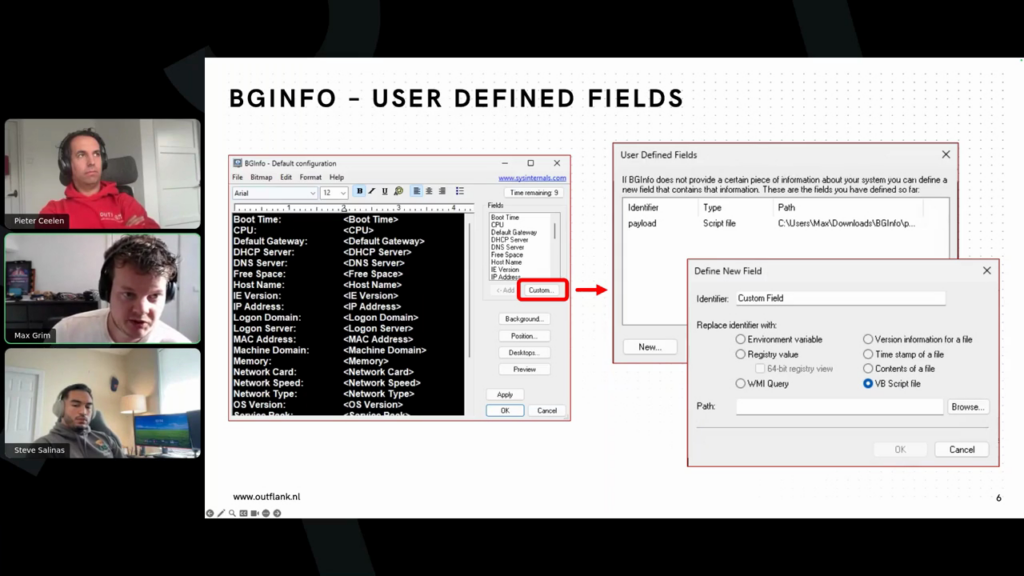
The integration of Large Language Models (LLMs) and artificial intelligence applications within offensive security operations and red teaming has led to a rapid evolution in attack methodologies. In this hands-on training, offensive security experts from Cobalt Strike and Outflank will demonstrate how harnessing these technologies can significantly enhance engagements. Topics covered will include: – Utilizing […]
Read More… from Offensive AI Training with Cobalt Strike and Outflank

We’re excited to announce the launch of a brand-new Cobalt Strike training course, created in collaboration between Fortra and Zero-Point Security. This unique partnership brings together the expertise of Cobalt Strike’s team with the field-tested training experience of Zero-Point Security to deliver an unmatched learning opportunity. Through this course users can learn how to use […]
Read More… from Get to Know Cobalt Strike: New Introductory Training
Take your red team skills to the next level with Cobalt Strike Certified Operator Training I (CSCO I), created through a collaboration between the experts at Zero Point Security and Cobalt Strike. Through these guided modules, you’ll explore the framework from the ground up—starting with setup and core commands, then advancing into post-exploitation, network bypass, […]
Read More… from Get Pricing: Cobalt Strike Certified Operator Training I (CSCO I)
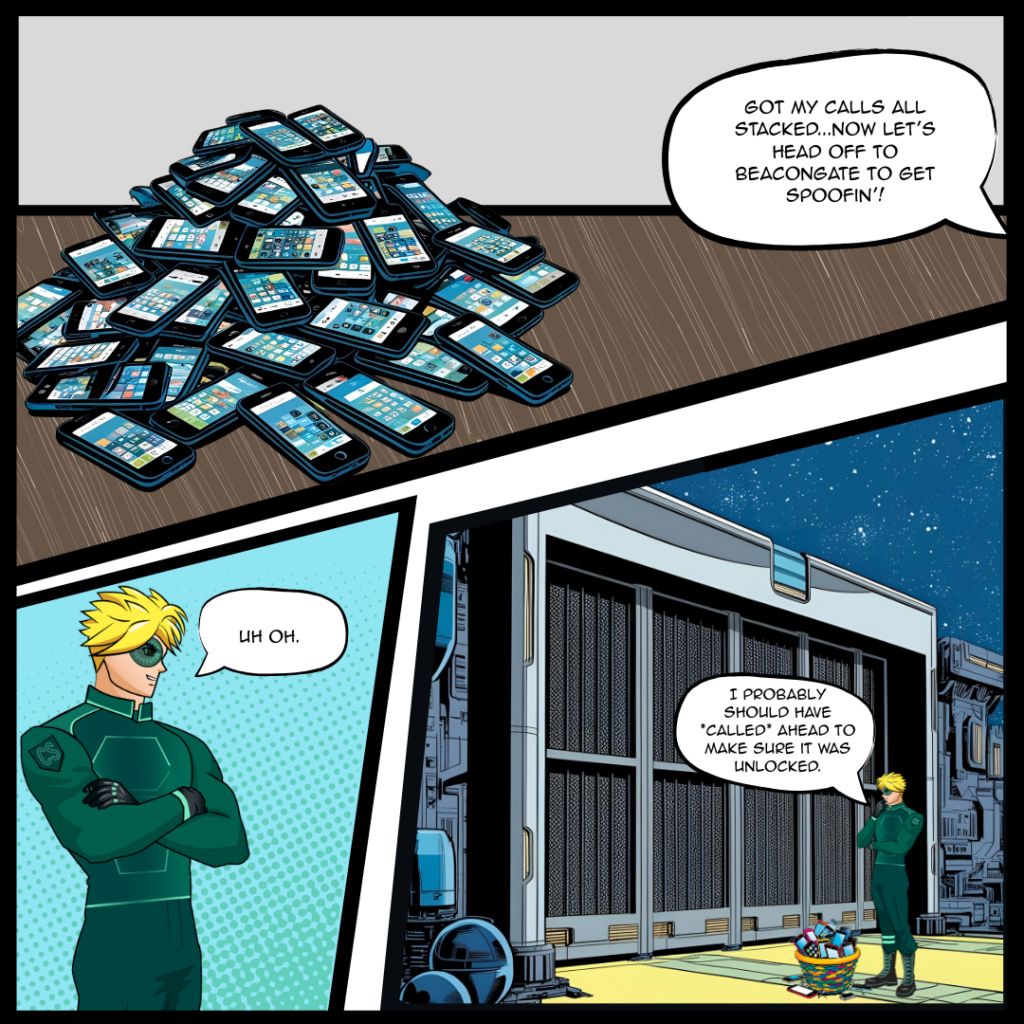
TL;DR: In this blog we’ll demonstrate how to instrument Beacon via BeaconGate and walk through our implementations of return address spoofing, indirect syscalls, and a call stack spoofing technique, Draugr, that are now available in Sleepmask-VS. Furthermore, we’ll provide tips and tricks for developers in getting set up with Sleepmask-VS so they can write their […]
Read More… from Dynamically Instrumenting Beacon With BeaconGate – For All Your Call Stack Spoofing Needs!