Industry Specific Adversary Insights Securing your business-critical assets and operations requires more than traditional protective measures; it requires seeing your organization the way an adversary does. This collection of offensive security use cases illustrates how organizations across critical sectors, like Government, Finance, and Healthcare, are doing exactly that. The industries differ, but there is a shared need […]
Product Line: Cobalt Strike
Offensive Security Use Cases
Securing your business-critical assets and operations requires more than traditional protective measures; it requires seeing your organization the way an adversary does. This collection of offensive security use cases illustrates how organizations across critical sectors, like Government, Finance, and Healthcare, are doing exactly that. The industries differ, but there is a shared need to test defenses, understand […]
CypherCon 2026

CypherCon is Wisconsin’s premier hacker and technology gathering, bringing together cybersecurity professionals, tech hobbyists, and curious learners for two days packed with creativity, innovation, and hands‑on experiences. Attendees can look forward to inspiring talks, immersive workshops, themed challenge areas, nostalgic hacker‑culture vibes, and sessions covering cybersecurity, AI, privacy, hacking methods, and much more. Join Fortra […]
OrangeCon 2026
OrangeCon is a community‑powered, non‑profit security gathering taking place in Amsterdam, bringing together cybersecurity practitioners of all backgrounds. The conference offers hands‑on training sessions to build practical skills, interactive community villages for meeting peers and sharing ideas, and presentations from some of the most respected security voices in the Netherlands—all centered around an open, friendly, […]
Fortra Cobalt Strike Demo Session – March 2026
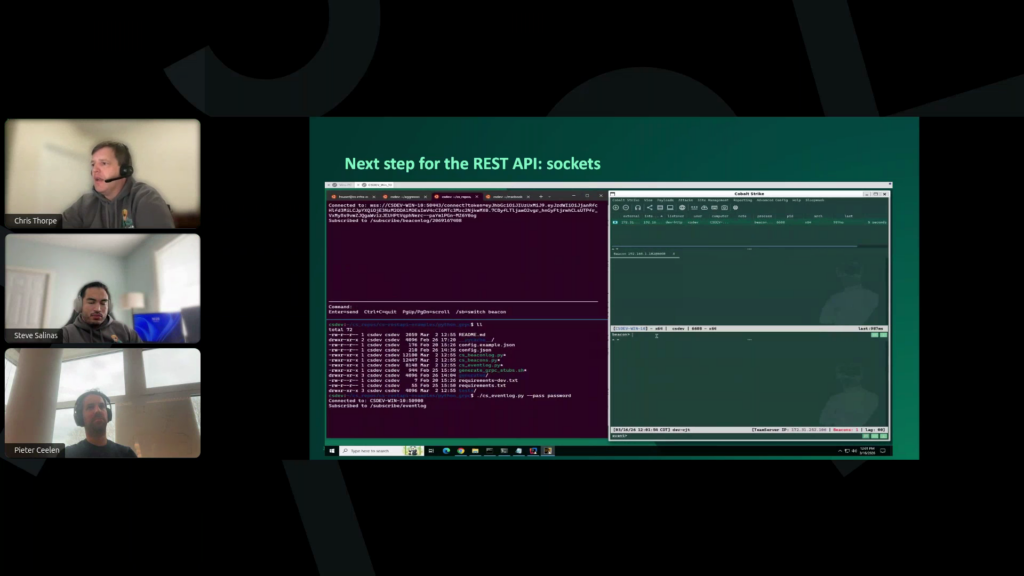
Unlock Next-Generation Adversary Simulation Capabilities Join our developers and researchers for our latest technical demo highlighting the 4.12 release, featuring cutting-edge post-exploitation techniques and adversary simulation strategies. Perfect for both seasoned operators and cybersecurity professionals seeking to understand the strategic philosophy behind this foundational red teaming framework. What you’ll experience: Why attend? Discover new approaches […]
Read More… from Fortra Cobalt Strike Demo Session – March 2026
Secure 360 Conference 2026

Secure360 has become the go‑to conference for professionals seeking well‑rounded education, collaboration, and fresh insights across the security and risk landscape. This event brings together experts and teams to explore critical topics including cybersecurity, governance, risk and compliance, physical security, business continuity, and overall professional growth. When:May 13-14 Where: Mystic Lake Center Prior Lake, Minnesota, […]
RSAC 2026 Conference – San Francisco

The RSA Conference USA is a leading global cybersecurity event, at the Moscone Center in San Francisco, bringing together thousands of industry professionals for high‑level keynotes, expert‑led sessions, hands‑on learning, and a large expo showcasing advanced security technologies, all unified under the 2026 theme, “The Power of Community.” When:March 23-26 Where: Moscone Center San Francisco, California, […]
Insomni’hack 2026
One of the world’s largest in‑person CTF competitions, drawing participants and experts from around the globe. It began as a modest hacking competition in 2008 and has since evolved into one of Switzerland’s and Europe’s major cybersecurity events. Hope to see you there! When:March 16-20 Where: SwissTech Convention Center Lausanne, Switzerland. Experts in Attendance: Samuel […]
Playing in the (Tradecraft) Garden of Beacon: Finding Eden

We have previously blogged about using BeaconGate to dynamically instrument Beacon at run time. However, one of BeaconGate’s limitations is that it is not applied throughout Beacon’s entire lifecycle. Specifically, it does not impact the reflective loading process. Hence, if an EDR is monitoring for unbacked VirtualAlloc or LoadLibrary calls, we cannot use BeaconGate to bypass it. To solve this problem, we must get our hands dirty with UDRL development. However, to […]
Read More… from Playing in the (Tradecraft) Garden of Beacon: Finding Eden
Manufacturing Sector Red Teaming Use Case
Background A high-tech manufacturing firm commissions a red team engagement to proactively test its readiness against targeted attacks. The firm is active in industrial automation and advanced components, and relies on proprietary designs, digital manufacturing workflows, and legacy OT systems. It understands its vulnerability to compromises aimed at IP theft and production disruption, and it […]