We will be making a small change to the Cobalt Strike infrastructure next week. This will not result in any downtime but will affect updates using old copies of the update application. TLS Certificate Update verify.cobaltstrike.com hosts a text file with SHA256 hashes for the licensed Cobalt Strike product and distribution packages for Windows, Linux […]
Read More… from Cobalt Strike Infrastructure Maintenance – January 2024
Cobalt Strike 4.9.1 is now available. This is an out of band update to fix an issue that was discovered in the 4.9 release that we felt would negatively impact customers as they start to roll out the release and for which there is no straightforward workaround. We also took the opportunity to address a […]
Read More… from Out of Band Update: Cobalt Strike 4.9.1
Cobalt Strike 4.9 is now available. This release sees an overhaul to Cobalt Strike’s post exploitation capabilities to support user defined reflective loaders (UDRLs), the ability to export Beacon without a reflective loader which adds official support for prepend-style UDRLs, support for callbacks in a number of built-in functions, a new in-Beacon data store and […]
Read More… from Cobalt Strike 4.9: Take Me To Your Loader
This is the second installment in a series revisiting the User-Defined Reflective Loader (UDRL). In part one, we aimed to simplify the development and debugging of custom loaders and introduced the User-Defined Reflective Loader Visual Studio (UDRL-VS) template. In this installment, we’ll build upon the original UDRL-VS loader and explore how to apply our own […]
Read More… from Revisiting the User-Defined Reflective Loader Part 2: Obfuscation and Masking
Core Impact empowers organizations to proactively minimize risk and protect critical assets by using the same techniques as today’s threat actors to assess their infrastructure’s security posture. This powerful platform provides a unified environment for managing all phases of the penetration testing process, from reconnaissance to reporting. Intuitive User Interface Core Impact features a thoughtfully […]
Read More… from Core Impact Datasheet
Beacon Object Files (BOFs) were introduced in Cobalt Strike 4.1 in 2020. Since their release, BOFs have played a key role in post-exploitation activities, surpassing Reflective DLLs, .NET assemblies, and PowerShell scripts. However, in our experience, many developers struggle with four primary pain points: In this blog post, we will tackle these difficulties by introducing […]
Read More… from Simplifying BOF Development: Debug, Test, and Save Your B(e)acon
This is a joint blog written by the Cobalt Strike and Outflank teams. It is also available on the Outflank site. Over the past few months there has been increasing collaboration and knowledge sharing internally between the Cobalt Strike and Outflank R&D teams. We are excited about the innovation opportunities made possible by this teamwork and […]
Read More… from Cobalt Strike and Outflank Security Tooling: Friends in Evasive Places
Fortra’s Advanced Red Team Bundle is comprised of three distinct enterprise-grade tools: Core Impact tests exploitation paths and lateral movement, Cobalt Strike enables advanced adversary tactics for Red Team operations, and Outflank Security Tooling (OST)provides a broad arsenal for evasive attack simulation. Additionally, this suite provides exclusive Cobalt Strike Research Labs access plus operator training. Ideal for dynamic proactive assessments, each […]
Read More… from Offensive Security Suite Datasheet
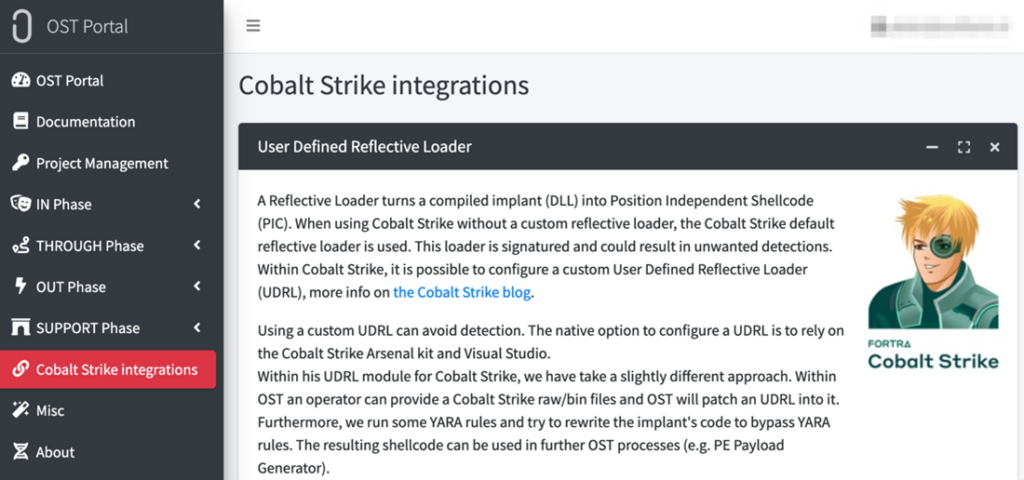
Cobalt Strike and Outflank Security Tooling (OST) are two red teaming solutions that enable operators to execute the diverse and varied tasks that each engagement requires. Cobalt Strike provides post-exploitation capabilities through its Beacon payload and malleable C2 framework, while OST is a broad arsenal of offensive security tools that covers the full attack chain with emphasis on evasion […]
Read More… from Red Team Suite Datasheet
Cobalt Strike helps organizations conduct advanced adversary simulations and Red Team engagements with ease, allowing your organization to effectively measure your security operations program and incident response capabilities. This on-demand Cobalt Strike demo includes a guided walkthrough of using Cobalt Strike in a small cyber range. The demo touches on several security topics to help […]
Read More… from Cobalt Strike Introduction and Demo