I spend a lot of time on the road in March and April—using my tools. During these months, I take careful notes of the usability issues I’d like to address and small tweaks that would make life better for Cobalt Strike’s hacker corps.
Today’s Cobalt Strike release is the result of notes and my first-hand experience from five different exercises. There’s a lot of great stuff here, particularly for Beacon users.
Beacon’s HTTP stager uses WinINet to communicate [even before this update]. This has a benefit. The HTTP stager will authenticate to a proxy server when stored credentials are available. Sometimes, the current process does not know the credentials needed to get through a web proxy server. Beacon’s HTTP stager now detects this situation and prompts the user for credentials. The dialog is the same one Internet Explorer uses. Between Beacon’s new HTTP stager and DNS stager—you now have the tools to defeat most tough egress restrictions.
Cobalt Strike’s Staged Executable Generator now gives you options to output Beacon as a raw blob of position independent shellcode. You also have the option to output a fully-staged Beacon as a PowerShell script too.
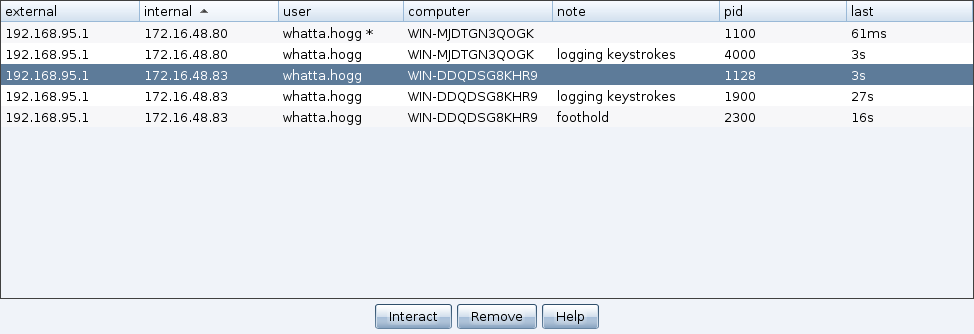
You may now assign a tiny note/label to each Beacon. This label is immediately visible to your teammates too. This makes Beacon management much easier.
Beacon’s process injection code now falls back to an alternate method when CreateRemoteThread fails. This means you’ll have an easier time injecting into explorer.exe and other processes across logon sessions.
Beacon’s session spawning now creates patsy processes in a suspended state. This allows you to use spawnto with almost any program you can think of. And hurrah! Beacon no longer uses notepad.exe as the default process to spawn and inject code into.
These changes are the highlights. For a full accounting of changes, give the Release Notes a read. Licensed Cobalt Strike users may use the update program to get the latest.
