Cobalt Strike 2.4 is now available. If you use Beacon for post-exploitation, you’ll find a lot to like in this release. Here’s the highlights:
Post-Exploitation Jobs
Beacon now supports long-running jobs. These are post-exploitation tasks that live in other processes and report information to Beacon as it becomes available.
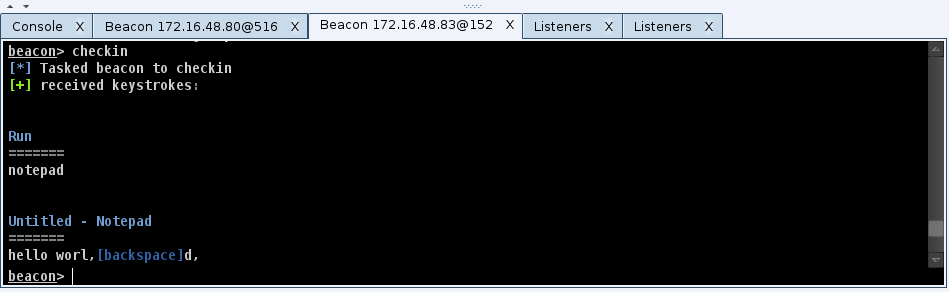
Beacon’s keystroke logger was rewritten to take advantage of jobs. You may now inject Beacon’s keystroke logger into an arbitrary x86 or x64 process and it will report keystrokes back to you. Use keylogger [pid] [x86|x64] to start collecting information from a process of interest.
I’ve also updated Beacon’s shell and powershell commands to run as jobs too. Do you have a PowerShell script that needs to run for days? That’s no problem. Beacon will drip output back to you as it becomes available.
Use Beacon’s jobs command to see which jobs are running in the current Beacon. Use jobkill to terminate a job.
The move to post-ex Jobs is good for Beacon long-term. Jobs isolate your Beacon from the processes where post-exploitation tasks take place. This removes the need for a dangerous migrate operation and it protects your Beacon should disaster strike one of the processes you’re collecting information from. This construct also favors features built as Reflective DLLs and PowerShell scripts. These are things that Beacon can import when you need to use them. This allows Beacon to gain new features, but also stay small, simple, and reliable.
Mimikatz
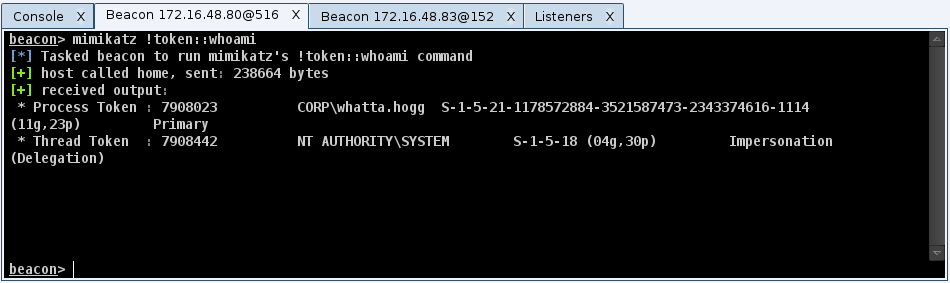
Beacon now integrates mimikatz. Use the mimikatz command to run a command through mimikatz’s command dispatcher. Beacon will even tab complete mimikatz commands for you.
Would you like a cup of coffee? Use mimikatz standard::coffee to get it. Would you like to beat minesweeper? Use mimikatz minesweeper::infos to reveal the map.
All joking aside, the amount of capability in mimikatz is incredible. Would you like to dump cached logon hashes? Use mimikatz !lsadump::cache. Use the ! to make mimikatz elevate to SYSTEM before it runs your command.
Would you like to dump plaintext passwords? Use mimikatz sekurlsa::wdigest. I’ve also created a wdigest command in Beacon to alias this for you.
This integration is very user friendly. Beacon will deploy an x64 or x86 mimikatz depending on the native architecture of the target system. Beacon will also attempt to secure the SE_DEBUG privilege for your mimikatz instance too.
As an aside, Beacon gained a hashdump command too. Similar to mimikatz, Beacon manages the x86/x64 and SE_DEBUG privilege madness for you. All you have to do is dump hashes and enjoy.
Foreign Listeners
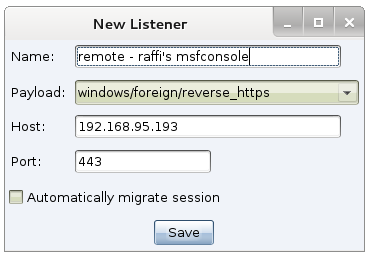
I’ve always considered session passing core to Cobalt Strike’s collaboration workflow. This release takes session passing to another level. Cobalt Strike now supports foreign listeners. These are listeners that reference a handler running in a remote Armitage, Cobalt Strike, or msfconsole instance.
If you need to pass a session to a friend, ask them for their payload type, host, and port. Create a foreign listener for them and then, you can pass accesses to them from a Beacon or any other Cobalt Strike feature that uses listeners.
These three items are just a taste of Cobalt Strike 2.4. For a full list of changes, you’ll want to consult the release notes. Licensed users may use the update program to get the latest.
