Cobalt Strike’s mission is to help security professionals emulate “advanced threat tactics” during their engagements. I’ve executed on this since the product’s 2012 release. Cobalt Strike 3.0 is the next iteration of this.
Cobalt Strike 3.0 is a ground-up rewrite of the client and server components in this product. Notably, Cobalt Strike no longer directly depends on the Metasploit Framework. Cobalt Strike 3.0 is a stand-alone platform for Adversary Simulations and Red Team Operations.
This release makes several strategic changes to support Cobalt Strike’s Red Team Operations and Adversary Simulation use cases. Here are the highlights…
Asynchronous Post Exploitation with Beacon
Beacon has completed its transition from stable lifeline to full-featured post-exploitation agent. This release includes features and workflows for user-exploitation at scale and a data model that populates itself with credentials and targets found with Beacon.
Logging and Reporting Designed for Red Team Operations
Logging and Reporting were completely overhauled. All logging now takes place on the team server. Each command is attributed to an operator. File uploads are hashed and the file hash is noted in the logs. Actions and output are captured whether a client is connected to the server or not. Cobalt Strike 3.0’s reports produce detailed timelines of red team activity and indicators of compromise.
Intuitive Named-pipe Pivoting
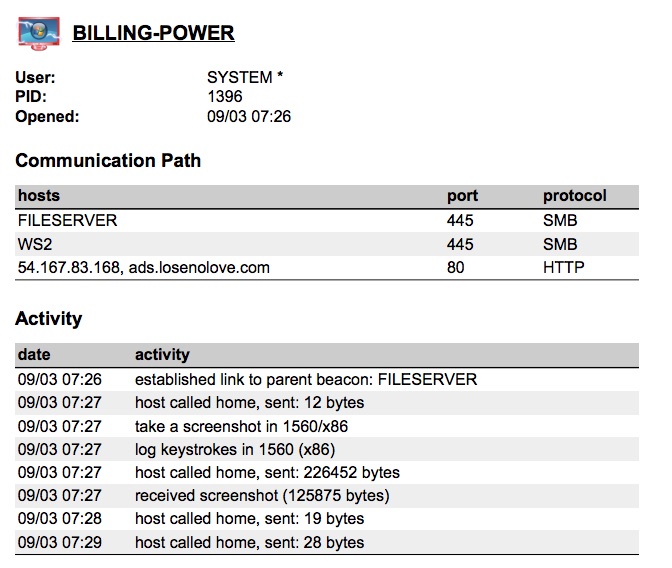
The SMB Beacon is a first-class part of Cobalt Strike’s workflows. This Beacon variant uses a named pipe to receive commands from and send output through a parent Beacon. This effectively allows you to chain Beacons to tightly control your communication path and egress systems/elevated processes through another Beacon’s channel. Cobalt Strike 3.0 supports the SMB Beacon with visualization that shows this chaining in a beautiful and intuitive way.
Target Acquisition and Lateral Movement
Cobalt Strike 3.0 also provides tools and workflows to support target acquisition and lateral movement with Beacon. The new net module uses Win32 APIs to discover and interrogate targets. Beacon also gained a port scanner that operates on target and reports intermediate results when Beacon checks in. The workflows to repurpose trust material and jump to a target are efficient and intuitive.
Advanced Threat Tactics Training
Finally, Cobalt Strike’s online training was refreshed for this 3.0 release. The Advanced Threat Tactics course is nearly six hours of material on the modern offensive process Cobalt Strike 3.0 supports.