Cobalt Strike 1.48 (02.27.14) is now available. This release is the byproduct of a very intense development cycle. The theme of this release is: details matter. Read on for a sense of what I mean by this.
Pivot Listeners
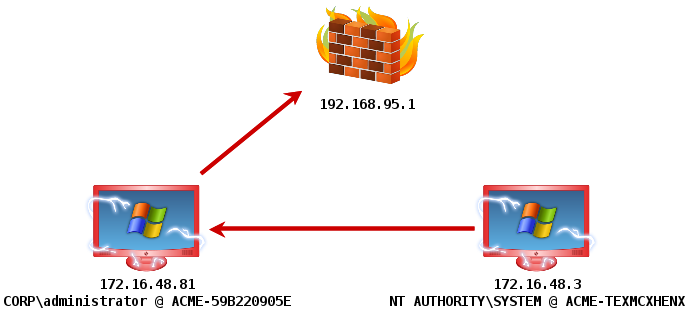
This Cobalt Strike update introduces pivot listeners. A pivot listener is a handler for a reverse payload that stages and tunnels through an existing Meterpreter session.
Because Cobalt Strike is built for targeted attacks, I always assume that my users are external to their target’s network. One way to keep a low profile is to limit how many connections you make to your command and control infrastructure. Unfortunately, a lot of post-exploitation actions you take will require a new session. Privilege escalation and lateral movement are prime examples.
A pivot listener allows you to spawn sessions through an existing Meterpreter session. Pivot listeners work anywhere you would use a normal Cobalt Strike listener. This gives you a way to limit your post-exploitation activity to one channel out of your target’s network.
Stager Tweaks
A topic that is near and dear to my heart is egress filtering. Cobalt Strike now uses a custom HTTP stager to deliver its Beacon. This custom stager takes steps to disguise itself as Internet Explorer. The native Metasploit Framework stager sends a blank User-Agent which is an opportunity for a proxy server to stop you or a defense team to catch you.
If you can get Beacon on a system, you’re just one step away from Meterpreter. Type ‘meterpreter’ and Beacon will act as a tunnel to stage and communicate with your session. Beacon’s ‘meterpreter’ command now uses a custom stager that avoids a popup from the Windows firewall.
Token Stealing and Privilege Escalation
This release also adds token stealing to Cobalt Strike’s Beacon payload. The usual repertoire of getuid, rev2self, and steal_token are present. The ability to steal tokens is key for lateral movement.
Before you can steal tokens, you need the ability to escalate your privileges. I’ve added getsystem to go from an administrator user to SYSTEM on a box, through Beacon.
UAC Bypass
Speaking of privilege escalation, this release adds bypassuac to Beacon as well. This command spawns a session in a process with elevated rights. This privilege escalation technique takes advantage of a loophole in the default UAC settings on Windows 7 and later. This command will not work if the current user is not in the Administrators group or if UAC is set to its highest setting.
The UAC Bypass attack has several steps to it. The last step is to get code execution through DLL search order hijacking of a program that automatically elevates itself to full rights. The public versions of this attack rely on a hijacking opportunity that works in Windows 7 only. Beacon’s UAC bypass uses different opportunities for Windows 7 and Windows 8.
Beacon’s UAC Bypass is also evasion friendly. The one DLL it drops to disk is made by Cobalt Strike’s Artifact Kit. All other UAC bypass logic happens in memory. And yes, the UAC Bypass cleans up after itself.
Details matter
Tools that succeed in production have to pay attention to details. Sometimes, new research makes it into Cobalt Strike. Other times, the work in this product is on the details. The small stuff that makes a big difference when you’re on an engagement.
You can grab a 21-day trial of Cobalt Strike. Licensed users should use the update program to get the latest. Consult the release notes file for a full list of changes.